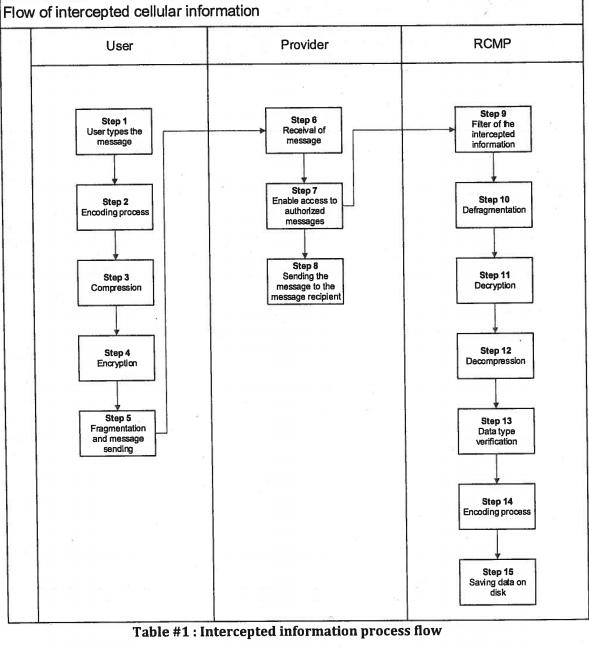
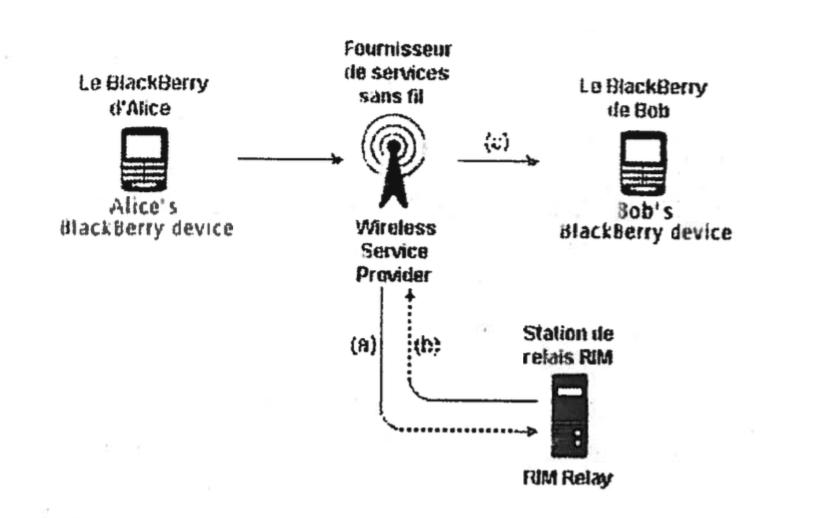
A high-level surveillance probe of Montreal’s criminal underworld shows that Canada’s federal policing agency has had a global encryption key for BlackBerry devices since 2010.The revelations are contained in a stack of court documents that were made public after members of a Montreal crime syndicate pleaded guilty to their role in a 2011 gangland murder. The documents shed light on the extent to which the smartphone manufacturer, as well as telecommunications giant Rogers, cooperated with investigators.According to technical reports by the Royal Canadian Mounted Police that were filed in court, law enforcement intercepted and decrypted roughly one million PIN-to-PIN BlackBerry messages in connection with the probe. The report doesn’t disclose exactly where the key — effectively a piece of code that could break the encryption on virtually any BlackBerry message sent from one device to another — came from. But, as one police officer put it, it was a key that could unlock millions of doors.Government lawyers spent almost two years fighting in a Montreal courtroom to keep this information out of the public record.And while neither the RCMP nor BlackBerry confirmed that the cellphone manufacturer handed over the global encryption key, and both fought against the defense’s attempt to release more information about their working relationship, the Crown prosecutors admitted that the federal police service had access to the key.And if the global key is still sitting on a server in the RCMP’s headquarters, the potential consequences could be significant. Although it wouldn’t offer police a backdoor into most of its government and business clients, who make up BlackBerry’s core constituency, it would mean that police enjoyed years of access to Canadians’ personal cellphones without the public being any the wiser.In a technical report attempting to underscore the significance of this technology and filed with the Superior Court of Quebec, the RCMP stated that ithad obtained “the key that would unlock the doors of all the houses of the people who use the provider’s services, and that, without their knowledge.”In light of a very public spat between the American FBI and iPhone manufacturer Apple about encryption, and whether or not consumer technology companies should comply with government orders to create new software to help release the keys to the proverbial castle, the Montreal case raises serious questions about the surveillance steps taken by police.“We don’t actually understand how the RCMP is using the laws that are developed for them,” said Christopher Parsons, a security researcher and postdoctoral fellow at the Citizen Lab. “An awful lot of Canadians would be surprised to learn that the RCMP would have this kind of capability.”This story is part of a joint investigation with Motherboard. Check them out for more details about how Canadian police obtained the master key to millions of cellphones.***On November 24, 2011, the body of Salvatore Montagna washed up on the snow-covered shore of an island in the frigid Assomption River, northeast of Montreal.Earlier that morning, local residents called 911. A man had jumped into the freezing water in a hail of gunfire, they told police. That man, Montagna, ended up catching at least one bullet on the way.Sal the Iron Worker, the dead man’s moniker, was vying to fill a power vacuum in the Montreal crime syndicate, according to police sources who spoke to Postmedia at the time. Reported talks to broker power in the family ended after a failed assassination attempt on one of Montagna’s main rivals, Raynald Desjardins.Montagna’s body, still warm and bleeding, washed up not far from the home where he had been before the shooting, which belonged to a Jack Simpson.But before they could even track down Simpson, who had a record for cocaine trafficking, Quebec investigators got a call from the Royal Canadian Mounted Police. They had been surveilling a cabal of suspected mobsters for more than a year.Operation Clemenza, as the RCMP probe was dubbed, happened to be following four individuals involved in the hit.Six men, including Simpson, were charged with first-degree murder. A seventh was charged with being an accessory after the fact. Desjardins pleaded guilty to a lower charge of conspiracy, but the rest of the accused went to court to fight. They wanted to know exactly how it was that the RCMP accessed the communications they had sent each other in the days leading up to the murder.Operation Clemenza didn’t bug the suspects’ phones or install microphones in the smoke detectors. Instead, the police had been surveilling Aaaaaaacounts, Shadow, Gâteau, and JJ — four pseudonyms assigned to BlackBerry Messenger accounts. Police linked up the screen names to real mobsters: Aaaaaaacounts was Pietro Magistrale, Shadow was Felice Racaniello, Gâteau was Steven Fracas, and JJ was Simpson.To intercept the messages, the cops went to the service providers — either the suspects’ cellphone company, Rogers; or BlackBerry itself.It’s not clear if the RCMP went to one, the other, or both, but what was revealed in the case is that the RCMP obtained assistance orders and sent “comfort letters” to BlackBerry — known during the court case as Research In Motion (RIM) — asking for their cooperation in the case, and that the company’s technicians consulted with the RCMP’s technical unit on these efforts to decrypt the phones.Assistance orders are legal authority, issued by the court, that can compel service providers — like Rogers, BlackBerry, and their ilk — to “assist” the police in carrying out other court orders, like wiretaps or search warrants. Comfort letters are harder to pin down. More than one lawyer consulted by VICE News were completely unfamiliar with the concept. But, according to defense lawyers who worked on the trial, they are essentially assurances provided by police to private individuals or corporations that the actions being requested of the individual or corporation are covered by an existing court order.“As part of a judicial authorization to intercept, the service provider will allow access to the information that transits on their network,” reads a technical report filed by the RCMP with the court. The report details that the data is sent directly to a secure room at RCMP headquarters.Obtaining the messages is only half of the equation. The data sitting there, on RCMP servers, would still be encrypted, a meaningless string of letters, numbers, and symbols. The only way to make that data legible would be to open it on a BlackBerry with the PIN address of its intended recipient or use BlackBerry’s global encryption code — the digital key that could break the lock on millions of private communications.
Desjardins pleaded guilty to a lower charge of conspiracy, but the rest of the accused went to court to fight. They wanted to know exactly how it was that the RCMP accessed the communications they had sent each other in the days leading up to the murder.Operation Clemenza didn’t bug the suspects’ phones or install microphones in the smoke detectors. Instead, the police had been surveilling Aaaaaaacounts, Shadow, Gâteau, and JJ — four pseudonyms assigned to BlackBerry Messenger accounts. Police linked up the screen names to real mobsters: Aaaaaaacounts was Pietro Magistrale, Shadow was Felice Racaniello, Gâteau was Steven Fracas, and JJ was Simpson.To intercept the messages, the cops went to the service providers — either the suspects’ cellphone company, Rogers; or BlackBerry itself.It’s not clear if the RCMP went to one, the other, or both, but what was revealed in the case is that the RCMP obtained assistance orders and sent “comfort letters” to BlackBerry — known during the court case as Research In Motion (RIM) — asking for their cooperation in the case, and that the company’s technicians consulted with the RCMP’s technical unit on these efforts to decrypt the phones.Assistance orders are legal authority, issued by the court, that can compel service providers — like Rogers, BlackBerry, and their ilk — to “assist” the police in carrying out other court orders, like wiretaps or search warrants. Comfort letters are harder to pin down. More than one lawyer consulted by VICE News were completely unfamiliar with the concept. But, according to defense lawyers who worked on the trial, they are essentially assurances provided by police to private individuals or corporations that the actions being requested of the individual or corporation are covered by an existing court order.“As part of a judicial authorization to intercept, the service provider will allow access to the information that transits on their network,” reads a technical report filed by the RCMP with the court. The report details that the data is sent directly to a secure room at RCMP headquarters.Obtaining the messages is only half of the equation. The data sitting there, on RCMP servers, would still be encrypted, a meaningless string of letters, numbers, and symbols. The only way to make that data legible would be to open it on a BlackBerry with the PIN address of its intended recipient or use BlackBerry’s global encryption code — the digital key that could break the lock on millions of private communications. For consumer-grade phones, the decryption key is in the company’s possession. BlackBerry, however, also offers the option to run their BlackBerry Enterprise Server (BES) which allows clients to run their own network of phones, and keep possession of their own decryption key. The RCMP’s technique likely would not work on those phones.The report acknowledges in black-and-white that, as part of the process, “the RCMP server performs the decryption of the message using the appropriate decryption key.”Judge Michael Stober, in a series of hearings in November 2015, was enraptured with a question: where did the key come from?The question proved crucial for the defense counsel, who fought to be able to verify that the supposed decryption of their clients’ messages were authentic, and done legally.The Crown prosecutor consistently refused to answer, telling the judge in a public hearing: “I’m going to refrain from any comment because we’re walking a very very fine thread. I don’t want to fall into a bear trap.”Neither the RCMP, nor BlackBerry ever confirmed where the global key actually came from and the documents shed little light on the matter. They also didn’t deny it.In fact, BlackBerry has recently signalled a willingness to deal with law enforcement on encryption, with company CEO John Chen writing last year that “we reject the notion that tech companies should refuse reasonable, lawful access requests.”“That’s the reality of it, that’s what we don’t want the general public to know.”
For consumer-grade phones, the decryption key is in the company’s possession. BlackBerry, however, also offers the option to run their BlackBerry Enterprise Server (BES) which allows clients to run their own network of phones, and keep possession of their own decryption key. The RCMP’s technique likely would not work on those phones.The report acknowledges in black-and-white that, as part of the process, “the RCMP server performs the decryption of the message using the appropriate decryption key.”Judge Michael Stober, in a series of hearings in November 2015, was enraptured with a question: where did the key come from?The question proved crucial for the defense counsel, who fought to be able to verify that the supposed decryption of their clients’ messages were authentic, and done legally.The Crown prosecutor consistently refused to answer, telling the judge in a public hearing: “I’m going to refrain from any comment because we’re walking a very very fine thread. I don’t want to fall into a bear trap.”Neither the RCMP, nor BlackBerry ever confirmed where the global key actually came from and the documents shed little light on the matter. They also didn’t deny it.In fact, BlackBerry has recently signalled a willingness to deal with law enforcement on encryption, with company CEO John Chen writing last year that “we reject the notion that tech companies should refuse reasonable, lawful access requests.”“That’s the reality of it, that’s what we don’t want the general public to know.”
Through the course of the trial, the defense managed to get the Crown to admit that this wasn’t just a key. It was the key. This was Blackberry’s global encryption key.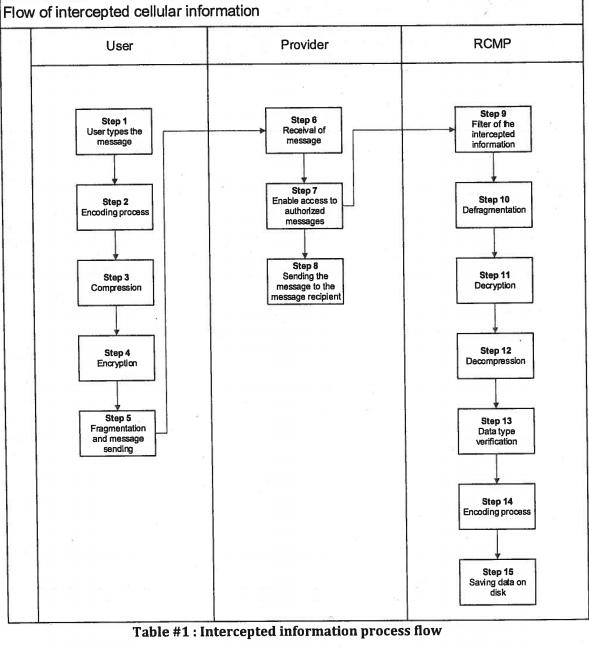 Many of the hearings about the global key happened on an ex parte basis, meaning that the defense counsel were not allowed to attend.Crown prosecutors pulled out a variety of excuses as to why the information about the origin of the key, and the exact nature of BlackBerry’s cooperation with the RCMP, should remain strictly private. In applications filed with the court, they cited privilege to avoid answering the court’s questions on that matter. They argued that disclosing the involvement of BlackBerry may “have a negative commercial impact on the company.” They claimed that admitting to BlackBerry’s involvement could compromise the police’s relationship with it, and other technology companies that may be called upon to help.At one point, the judge sided with the defense in ordering that the RCMP release the key itself to the defense, which would likely mean that the key — the one that can open millions of digital locks — would be released publicly. That request was later dropped.
Many of the hearings about the global key happened on an ex parte basis, meaning that the defense counsel were not allowed to attend.Crown prosecutors pulled out a variety of excuses as to why the information about the origin of the key, and the exact nature of BlackBerry’s cooperation with the RCMP, should remain strictly private. In applications filed with the court, they cited privilege to avoid answering the court’s questions on that matter. They argued that disclosing the involvement of BlackBerry may “have a negative commercial impact on the company.” They claimed that admitting to BlackBerry’s involvement could compromise the police’s relationship with it, and other technology companies that may be called upon to help.At one point, the judge sided with the defense in ordering that the RCMP release the key itself to the defense, which would likely mean that the key — the one that can open millions of digital locks — would be released publicly. That request was later dropped.
The idea of publishing the key was one that led BlackBerry to object.Alan Treddenick, Director of National Security and Law Enforcement Liaison at BlackBerry, swore in an affidavit that if the court ordered the RCMP to hand over details about the encryption key, or the key itself, in its possession, it would “potentially impact relationships with other end-users and law enforcement criminal investigations globally for all foreign countries that BlackBerry operates and provides communication services.”During the hearings, Crown attorney Robert Rouleau asked RCMP Inspector Mark Flynn: would the disclosure of this information about the global key jeopardize ongoing investigations?“We have several investigations ongoing right now, varying from individual homicides, organized crime homicides and organized crime and drug investigations occurring in various locations in Canada today [where] our capabilities in this environment are a significant factor,” Flynn said, according to a 2015 transcript filed with the court.Rouleau even admitted to the judge, during one ex parte hearing, that his own phone would be vulnerable to the type of intrusion the RCMP used on the targets of the investigation.“I’m a dead chicken. That’s the reality of it, that’s what we don’t want the general public to know,” Rouleau said.“The exact same sorts of tools can be used in countries that don’t have the same rule of law that we do.”
Both the defense and the Crown came to an agreement in the court documents — the RCMP used the global key. As defense lawyer Michael Lacy phrased it: “You have to have the proprietary or intellectual property of RIM/BlackBerry, wherever it comes from, in order to make sense of an encrypted PIN to PIN communication.”The court ultimately ordered the Crown to disclose to the defense virtually everything about the global key and how they obtained it, save for the key itself. The Crown appealed, and the next phase of the legal saga was scheduled for March 30, 2016.***On Wednesday, March 30, the seven men accused of the murder walked into a courtroom in Laval, just north of Montreal. Six pleaded guilty to conspiracy to commit murder, and the seventh confessed to being an accessory after the fact.At almost exactly the same time, the lawyers fighting on their behalf to reveal the details of this global key walked past the giant stone columns of the Quebec Court of Appeal in Montreal’s Old Port and informed a three-judge panel that, in light of the pleas, the appeal would be discontinued. That means that Judge Stober’s ruling, that the Crown must disclose how BlackBerry cooperated to help the RCMP crack the suspects’ communications and how the RCMP obtained the global key, would never be fulfilled.
Lacy, one of the defense lawyer in the case, says the end of the appeal leaves a litany of unanswered questions.“There were documents that we filed on the motion that made it clear that RIM is, and was, actively involved in facilitating the orders,” he told VICE News.What remains a mystery, he said, is how.“We were satisfied based on the evidence adduced at the hearing, and our own inquiries, that you had to have the actual global encryption key,” he said. As to where it came from? “That’s very much an open question.”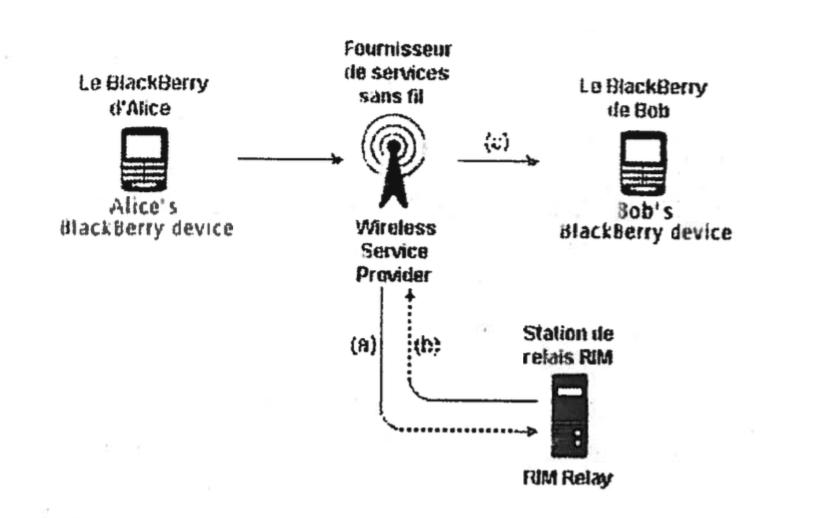 BlackBerry’s Canadian and American offices declined to comment for this story. A spokesperson for Rogers declined to address the case directly, instead sending a prepared statement stating that they protect their customers’ privacy and only cooperate with valid legal requests.Minister of Public Safety Ralph Goodale would not speak to the specifics of the case or Operation Clemenza during a phone conversation with VICE News, nor would he comment on the appropriateness of the RCMP obtaining the global decryption key, but did say he was familiar with the operation. Citing the ongoing public debate in the United States over the FBI’s request to unlock the cellphone that belonged to the San Bernardino shooters, Goodale said that now is the time for discussions about encryption and privacy to be had.“Where is the proper intersection, or boundary line if you will, between the proper requirements of public safety and the proper requirements of privacy? And where does society want to define that line, and that discussion has not been had yet?” Goodale said. “That discussion has to be had.”Goodale went on to say that his government will be introducing legislation to establish an independent Parliamentary review committee for Canada’s intelligence collection services before the Summer, although did not specify whether that body would also be tasked with overseeing the RCMP.The RCMP turned down an interview with someone from either of the units involved with Operation Clemenza, and declined to talk specifically about the operation or the BlackBerry global encryption key, but did send a statement regarding encryption in general.“Using encryption to secure data and communications assists in crime prevention but may also inhibit the lawfully authorized interception of communications and evidence gathering in national security and criminal investigations,” reads the RCMP statement. “These are complex challenges which the RCMP continues to study. The RCMP encourages public discourse with Canadians as public policy continues to take shape on the issue of encryption.”The statement goes on to detail how the RCMP can obtain wiretap warrants and intercept communications. “However, there is no specific power in the Criminal Code to compel a third party to decrypt or develop decryption tools, nor is there any requirement for telecommunications services to provide these services,” the statement concludes.Lacy, the defense lawyer, calls that “misleading.” He says the Criminal Code is rife with authorities to compel service providers to aid in investigations. He adds that it’s an “open question” as to whether the global key was handed over by court order.Even so, the details revealed by the case are bad news for the company, which was once lauded as an industry leader in terms of privacy and encryption.“The exact same sorts of tools can be used in countries that don’t have the same rule of law that we do,” Parsons, the Citizen Lab researcher, said. “The fact that it’s a weak cryptographic system means that it’s a weak cryptographic system for everyone in the world.”In the end, after two years of wrangling over one of Canada’s most high-level and secretive surveillance programs, nobody will stand trial for firing the shot that killed Salvatore Montagna.
BlackBerry’s Canadian and American offices declined to comment for this story. A spokesperson for Rogers declined to address the case directly, instead sending a prepared statement stating that they protect their customers’ privacy and only cooperate with valid legal requests.Minister of Public Safety Ralph Goodale would not speak to the specifics of the case or Operation Clemenza during a phone conversation with VICE News, nor would he comment on the appropriateness of the RCMP obtaining the global decryption key, but did say he was familiar with the operation. Citing the ongoing public debate in the United States over the FBI’s request to unlock the cellphone that belonged to the San Bernardino shooters, Goodale said that now is the time for discussions about encryption and privacy to be had.“Where is the proper intersection, or boundary line if you will, between the proper requirements of public safety and the proper requirements of privacy? And where does society want to define that line, and that discussion has not been had yet?” Goodale said. “That discussion has to be had.”Goodale went on to say that his government will be introducing legislation to establish an independent Parliamentary review committee for Canada’s intelligence collection services before the Summer, although did not specify whether that body would also be tasked with overseeing the RCMP.The RCMP turned down an interview with someone from either of the units involved with Operation Clemenza, and declined to talk specifically about the operation or the BlackBerry global encryption key, but did send a statement regarding encryption in general.“Using encryption to secure data and communications assists in crime prevention but may also inhibit the lawfully authorized interception of communications and evidence gathering in national security and criminal investigations,” reads the RCMP statement. “These are complex challenges which the RCMP continues to study. The RCMP encourages public discourse with Canadians as public policy continues to take shape on the issue of encryption.”The statement goes on to detail how the RCMP can obtain wiretap warrants and intercept communications. “However, there is no specific power in the Criminal Code to compel a third party to decrypt or develop decryption tools, nor is there any requirement for telecommunications services to provide these services,” the statement concludes.Lacy, the defense lawyer, calls that “misleading.” He says the Criminal Code is rife with authorities to compel service providers to aid in investigations. He adds that it’s an “open question” as to whether the global key was handed over by court order.Even so, the details revealed by the case are bad news for the company, which was once lauded as an industry leader in terms of privacy and encryption.“The exact same sorts of tools can be used in countries that don’t have the same rule of law that we do,” Parsons, the Citizen Lab researcher, said. “The fact that it’s a weak cryptographic system means that it’s a weak cryptographic system for everyone in the world.”In the end, after two years of wrangling over one of Canada’s most high-level and secretive surveillance programs, nobody will stand trial for firing the shot that killed Salvatore Montagna.
Advertisement
Advertisement
Advertisement

Advertisement
Advertisement

Advertisement
Through the course of the trial, the defense managed to get the Crown to admit that this wasn’t just a key. It was the key. This was Blackberry’s global encryption key.
The idea of publishing the key was one that led BlackBerry to object.Alan Treddenick, Director of National Security and Law Enforcement Liaison at BlackBerry, swore in an affidavit that if the court ordered the RCMP to hand over details about the encryption key, or the key itself, in its possession, it would “potentially impact relationships with other end-users and law enforcement criminal investigations globally for all foreign countries that BlackBerry operates and provides communication services.”
Advertisement
Both the defense and the Crown came to an agreement in the court documents — the RCMP used the global key. As defense lawyer Michael Lacy phrased it: “You have to have the proprietary or intellectual property of RIM/BlackBerry, wherever it comes from, in order to make sense of an encrypted PIN to PIN communication.”The court ultimately ordered the Crown to disclose to the defense virtually everything about the global key and how they obtained it, save for the key itself. The Crown appealed, and the next phase of the legal saga was scheduled for March 30, 2016.
Advertisement
Lacy, one of the defense lawyer in the case, says the end of the appeal leaves a litany of unanswered questions.“There were documents that we filed on the motion that made it clear that RIM is, and was, actively involved in facilitating the orders,” he told VICE News.What remains a mystery, he said, is how.“We were satisfied based on the evidence adduced at the hearing, and our own inquiries, that you had to have the actual global encryption key,” he said. As to where it came from? “That’s very much an open question.”
Advertisement