Image: Shutterstock
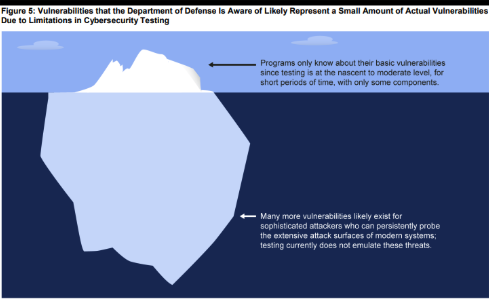
America’s newest weapon systems—the F-35 jet, missile systems, and other cutting edge machines—aren’t ready to withstand cyber attacks and can be “easily hacked” using “basic tools.”That’s the finding of a new report from the Government Accountability Office (GAO)—a non-partisan agency that investigates issues at Congress’ request. In a report published on Tuesday, the GAO found “mission-critical cyber vulnerabilities in nearly all weapon systems that were under development.” According to the report, software-enabled functions that are “potentially susceptible to compromise” include targeting missiles and flying aircraft.Just like how the internet has become a part of everyone’s everyday life, it’s also an integral part of the Pentagon’s weapon systems. The F-35’s pilot helmet alone connects to a complicated data feed from various outside systems. That connectivity has created new vulnerabilities, and the GAO report suggests that the Pentagon has done a terrible job of accounting for those vulnerabilities.Another team easily took control of the operator’s terminal for an unspecified weapon system and watched in real-time as the operators responded to the hackers’ disruptions. “Another test team reported that they caused a pop-up message to appear on users’ terminals instructing them to insert two quarters to continue operating. Multiple test teams reported that they were able to copy, change, or delete system data including one team that downloaded 100 gigabytes.” The GAO has been warning the Pentagon about the software vulnerabilities in weapon systems as far back as 1997, but the military has done little to fix the problems."It points to a potential point of catastrophic failure, which an adversary could exploit in a war,” Peter Singer, a strategist at the New America think tank, and a former researcher for the Council on Foreign Relations, told Motherboard in an email. “The sad thing is that this risk was easily predictable; indeed it has been warned about for literally years.”According to Chaplain, part of the reason the Pentagon been slow to react is systemic.“There’s a culture at the [Pentagon] where the extent of this problem really isn’t appreciated,” Chaplain said on the GAO’s podcast. “Sometimes, if there’s a vulnerability, it might be classified and not everyone on a program knows about it. So sharing what’s out there and what to do about it can be difficult.”Besides software vulnerabilities, the Pentagon wasn’t practicing basic internet security hygiene, the GAO report found. “Poor password management was a common problem in the test reports we reviewed,” the report said. “One test report indicated that the test team was able to guess an administrator password in nine seconds. Multiple weapon systems used commercial or open source software, but did not change the default password when the software was installed.”In another test, simply scanning a weapons system for vulnerabilities was enough to shut parts of the system down. “One test had to be stopped due to safety concerns after the test team scanned the system,” the GAO said. “This is a basic technique that most attackers would use and requires little knowledge or expertise.”The GAO said that most of the officials it met with felt their weapons systems were secure, even if they’d never been tested. Others claimed the tests were unrealistic, saying that the GAO teams had too much prior knowledge of the platforms they were attacking.“People look at weapons and think that they’re automatically very different than their own home computer or the business networks we see getting attacked everyday,” Chaplain said on the GAO podcast. “But they’re not so different […] they have the same components.”“It looks grim unless they see this as a wake up call.”Get six of our favorite Motherboard stories every day by signing up for our newsletter.
The GAO has been warning the Pentagon about the software vulnerabilities in weapon systems as far back as 1997, but the military has done little to fix the problems."It points to a potential point of catastrophic failure, which an adversary could exploit in a war,” Peter Singer, a strategist at the New America think tank, and a former researcher for the Council on Foreign Relations, told Motherboard in an email. “The sad thing is that this risk was easily predictable; indeed it has been warned about for literally years.”According to Chaplain, part of the reason the Pentagon been slow to react is systemic.“There’s a culture at the [Pentagon] where the extent of this problem really isn’t appreciated,” Chaplain said on the GAO’s podcast. “Sometimes, if there’s a vulnerability, it might be classified and not everyone on a program knows about it. So sharing what’s out there and what to do about it can be difficult.”Besides software vulnerabilities, the Pentagon wasn’t practicing basic internet security hygiene, the GAO report found. “Poor password management was a common problem in the test reports we reviewed,” the report said. “One test report indicated that the test team was able to guess an administrator password in nine seconds. Multiple weapon systems used commercial or open source software, but did not change the default password when the software was installed.”In another test, simply scanning a weapons system for vulnerabilities was enough to shut parts of the system down. “One test had to be stopped due to safety concerns after the test team scanned the system,” the GAO said. “This is a basic technique that most attackers would use and requires little knowledge or expertise.”The GAO said that most of the officials it met with felt their weapons systems were secure, even if they’d never been tested. Others claimed the tests were unrealistic, saying that the GAO teams had too much prior knowledge of the platforms they were attacking.“People look at weapons and think that they’re automatically very different than their own home computer or the business networks we see getting attacked everyday,” Chaplain said on the GAO podcast. “But they’re not so different […] they have the same components.”“It looks grim unless they see this as a wake up call.”Get six of our favorite Motherboard stories every day by signing up for our newsletter.
Advertisement
The Pentagon didn’t bother to change the default passwords on “multiple” weapon systems using commercial or open source software, the report says, essentially treating cutting edge military tech like a lazy person treats a new internet router.“The [Pentagon’s] own testing shows they can be pretty easily hacked,” Cristina T. Chaplain, the lead author of the report, said on the GAO’s podcast on Tuesday. “Until recently, [the Pentagon] was not prioritizing cybersecurity in the development process. Over the past decade or so, [the Pentagon] has really emphasized networking [the weapons systems] and bringing them together which increases the span of their challenge in terms of cyber.”It was shockingly easy for the GAO’s team to hack into the Pentagon’s weapon systems and take complete control. “In one case, it took a two-person test team just one hour to gain initial access to a weapon system and one day to gain full control of the system they were testing,” the GAO report said."The [Pentagon’s] own testing shows they can be pretty easily hacked"
Advertisement
Read More: The Cybersecurity World Is Debating WTF Is Going on With Bloomberg’s Chinese Microchip Stories
Advertisement
