Image: Shutterstocl
On Tuesday, a wide range of private businesses reportedly suffered ransomware attacks. Although it is not clear if every case is connected, at least several of them appear to be related to the same strain of malware.The attacks bear some resemblance to the recent WannaCry outbreak, in which thousands of computer systems were locked down with ransomware around the world.Motherboard has seen several reports of infections shared by victims on Twitter. We were not able to immediately confirm the veracity of the reports, but several security researchers and firms also reported the attacks."We are seeing several thousands of infection attempts at the moment, comparable in size to Wannacry's first hours," Costin Raiu, a security researcher at Kaspersky Lab, told Motherboard in an online chat.Judging by photos posted to Twitter and images provided by sources, many of the alleged attacks involved a piece of ransomware that displays red text on a black background, and demands $300 worth of bitcoin."If you see this text, then your files are no longer accessible, because they are encrypted," the text reads, according to one of the photos. "Perhaps you are busy looking for a way to recover your files, but don't waste your time. Nobody can recover your files without our decryption service."According to a tweet from anti-virus company Avira, the attacks were taking advantage of the EternalBlue exploit previously leaked by the group known as The Shadow Brokers. Symantec, another security firm, later tweeted that its analyst "confirmed" that the outbreak spread using EternalBlue. (Motherboard could not independently confirm this at the time of writing).EternalBlue is the same exploit used in the WannaCry attacks; it takes advantage of a vulnerability in the SMB data-transfer protocol, and Microsoft has since patched the issue. However, whether customers apply that patch is another matter.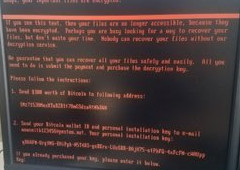 Spanish outlet El Confidencial reported hackers had hit the Madrid office of DLA Piper, a global law firm. One person familiar with the attack sent Motherboard a photo of an infected computer the source said was in DLA Piper's Washington DC office, and claimed that employees had been told to leave their workstations (neither the DC nor Madrid office immediately responded to phone calls).A customer of DLA Piper told Motherboard they could not connect to the portal used to host sensitive documents. Motherboard confirmed that the portal is currently inaccessible.Hackers also attacked a Ukrainian media company, according to a local report from 24tv, one of the company's outlets.UK-based Global advertising and public relations firm WPP tweeted on Tuesday it had suffered a "cyber attack." A source told Motherboard that MediaCom, a UK company owned by WPP, had been infected with ransomware. MediaCom did not immediately respond to a request for comment.The hackers who control the email account posted in the ransomware message did not immediately respond to a request for comment.Security researchers from Kaspersky Lab reported that the ransomware hit Russia, Ukraine, Spain, France, among others. Several people on Twitter reported witnessing or hearing reports of the outbreak in their respective countries, and across a wide range of industries. Companies around the world also reported computer outages.Hours after the initial outbreak, Rob Wainwright, the executive director of Europol said in a tweet the European law enforcement agency was "urgently responding" to "another major ransomware attack" across Europe.Chris Sistrunk, a security researcher at Mandiant, said that it looks like there's "another global outbreak attack."This is a developing story and we will update it as we learn of new details.This story has been updated to clarify Kaspersky Lab's analysis. The firm initially said the ransomware was a strain of Petya, but now believes it's something different.
Spanish outlet El Confidencial reported hackers had hit the Madrid office of DLA Piper, a global law firm. One person familiar with the attack sent Motherboard a photo of an infected computer the source said was in DLA Piper's Washington DC office, and claimed that employees had been told to leave their workstations (neither the DC nor Madrid office immediately responded to phone calls).A customer of DLA Piper told Motherboard they could not connect to the portal used to host sensitive documents. Motherboard confirmed that the portal is currently inaccessible.Hackers also attacked a Ukrainian media company, according to a local report from 24tv, one of the company's outlets.UK-based Global advertising and public relations firm WPP tweeted on Tuesday it had suffered a "cyber attack." A source told Motherboard that MediaCom, a UK company owned by WPP, had been infected with ransomware. MediaCom did not immediately respond to a request for comment.The hackers who control the email account posted in the ransomware message did not immediately respond to a request for comment.Security researchers from Kaspersky Lab reported that the ransomware hit Russia, Ukraine, Spain, France, among others. Several people on Twitter reported witnessing or hearing reports of the outbreak in their respective countries, and across a wide range of industries. Companies around the world also reported computer outages.Hours after the initial outbreak, Rob Wainwright, the executive director of Europol said in a tweet the European law enforcement agency was "urgently responding" to "another major ransomware attack" across Europe.Chris Sistrunk, a security researcher at Mandiant, said that it looks like there's "another global outbreak attack."This is a developing story and we will update it as we learn of new details.This story has been updated to clarify Kaspersky Lab's analysis. The firm initially said the ransomware was a strain of Petya, but now believes it's something different.
Read more: Don't Draw the Wrong Conclusions from the WannaCry Ransomware Outbreak
Advertisement
After initially believing that the ransomware was a strain of the well-known Petya, Raiu told Motherboard that "it seems to be a new thing indeed." Kaspersky Lab is calling it NotPetya.Researchers at MalwareHunterTeam, a research group focused on ransomware, told Motherboard in a Twitter direct message they believed the attack was from the same malware family as the one initially identified by Raiu. Like other types of ransomware, the malware seen Tuesday encrypts files on a user's system; hackers say they will give victims the encryption key in exchange for bitcoin.
Advertisement
Advertisement

