Yoshina/Flickr
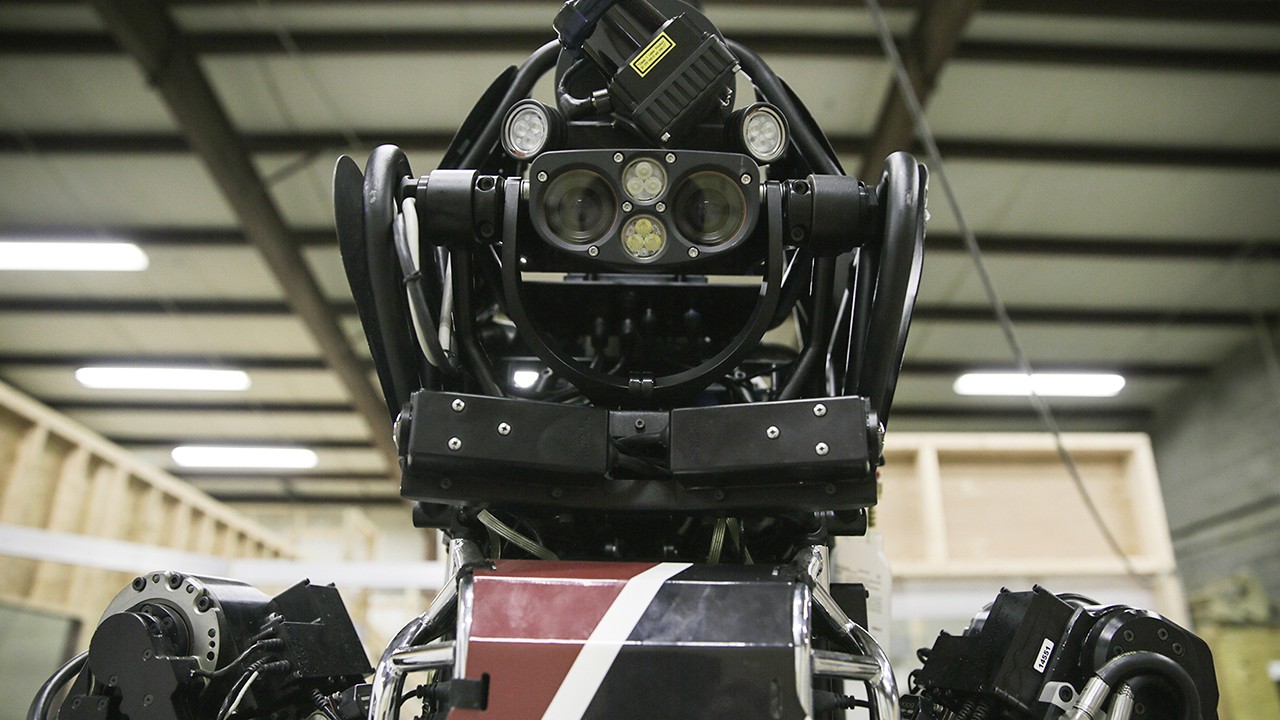
In the cult Japanese anime Patlabor, humanity has invented giant worker robots called "Labors," but a couple of them go haywire and investigators eventually find out there was malware implanted in the robots' new operating system update, which their company made. With the rise of consumer and household robots, that dystopian scenario might be closer to reality than we realize.In fact, according to two security researchers who have studied a dozen household robots, most of the robots you can buy today have common bugs that potentially makes them hackable.Cesar Cerrudo and Lucas Apa said they looked into the security of the SoftBank Robotics' NAO and Pepper, the UBTECH Robotics' Alpha 1S and Alpha 2, the ROBOTIS' OP2 and THORMANG3, among others, and found more than 50 bugs in their ecosystem.Read more: How This Internet of Things Stuffed Animal Can Be Remotely Turned Into a Spy DeviceThese robots have so many vulnerabilities, Cerrudo said, that he wouldn't have them always on if he owned one."If you are in the same network as the robot, then you can compromise it," Cerrudo told Motherboard in a phone call. "I will have a robot at home and the office but I will unplug it at night and also when I'm not around I won't leave the robot alone—I won't trust it."These humanoid robots they studied can be programmable, such as the NAO and the Alpha 1S, and are designed as family companions, but also as rescue robots, as it's the case with the THORMAN, which was part of the DARPA Robotics Challenge.Cerrudo and Apa, who work for the security firm IOActive, said the bugs are still in the process of being fixed, so they can't reveal too many details on the vulnerabilities they found. The two also said that their tests for now are not a "deep, extensive security audit."In a white paper they published on Wednesday, however, they list some of the bugs they found, without saying which robots in particular they affect. Some of them, as the two researchers said, are "common problems," such as not using encryption or not implementing it correctly, using default passwords, authentication systems that can be bypassed without a password, allowing unauthorized updates to the operating systems, and leak of private data.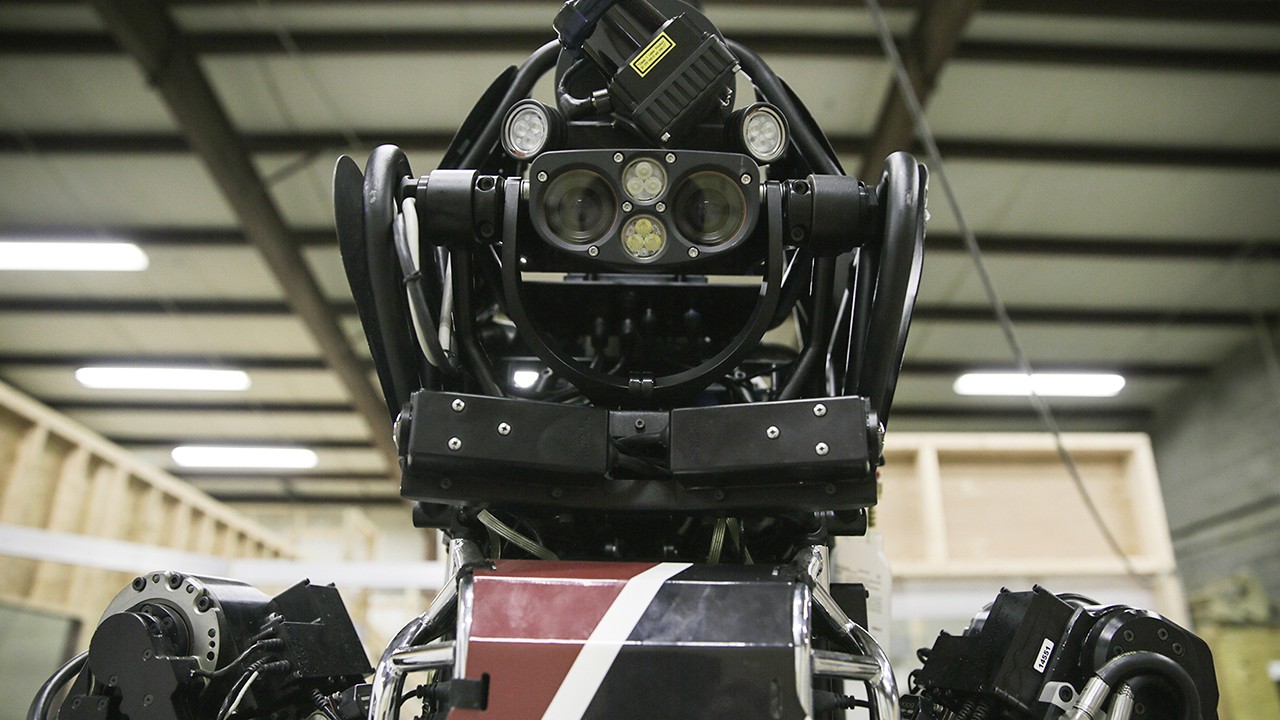 The researchers are hoping their paper is a wake-up call, showing that "it's time for all robot vendors to take immediate action in securing their technologies," as they wrote. They're not the first ones to sound the alarm. For years, several academics and researchers have looked into the security and privacy risks of household robots.While there haven't been any incidents where hacked robots caused physical damage yet, we have already seen data breaches and other more traditional security issues. Just this week, Motherboard revealed that a company that makes internet-connected stuffed animals left customer data exposed online, and these toys could even be turned into bugging devices. Last year, researchers also showed that it'd be possible to hack surgical robots, putting lives in danger.All in all, there's still no reason to fear the rise of Skynet, or robots that can harm people in any way, but before we put robots in all households we should probably make sure they can't be hacked because they use "123456" as password.Get six of our favorite Motherboard stories every day by signing up for our newsletter.
The researchers are hoping their paper is a wake-up call, showing that "it's time for all robot vendors to take immediate action in securing their technologies," as they wrote. They're not the first ones to sound the alarm. For years, several academics and researchers have looked into the security and privacy risks of household robots.While there haven't been any incidents where hacked robots caused physical damage yet, we have already seen data breaches and other more traditional security issues. Just this week, Motherboard revealed that a company that makes internet-connected stuffed animals left customer data exposed online, and these toys could even be turned into bugging devices. Last year, researchers also showed that it'd be possible to hack surgical robots, putting lives in danger.All in all, there's still no reason to fear the rise of Skynet, or robots that can harm people in any way, but before we put robots in all households we should probably make sure they can't be hacked because they use "123456" as password.Get six of our favorite Motherboard stories every day by signing up for our newsletter.
Advertisement
Advertisement