Image: JACK GUEZ/AFP via Getty Images)
Hacking. Disinformation. Surveillance. CYBER is Motherboard's podcast and reporting on the dark underbelly of the internet.
Advertisement
Advertisement
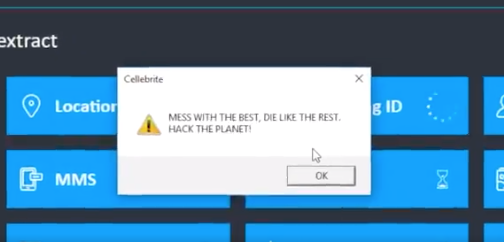
Cellebrite did not immediately respond to a request for comment. In their analysis of the device, Signal researchers also found that it contained packages signed by Apple, and likely extracted from the Windows installer for iTunes version 12.9.0.167. According to Marlinspike, this could be a copyright violation. Subscribe to our cybersecurity podcast, CYBER.Do you work for Cellebrite? Or do you research vulnerabilities on iPhones and Android devices? We’d love to hear from you. Using a non-work phone or computer, you can contact Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, lorenzofb on Wickr, OTR chat at lorenzofb@jabber.ccc.de, or email lorenzofb@vice.com

