Image: Flickr, Sebastien Launay
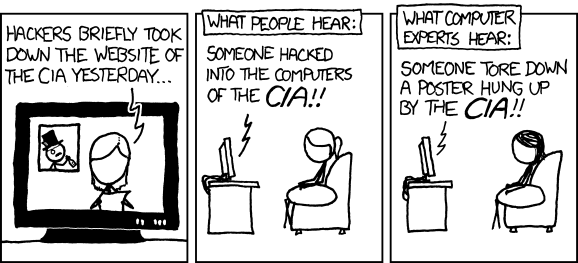
A group of researchers only needed $104 and 8 hours of Amazon's cloud computing power to hack the NSA's website. And their feat was made possible by a bug that, ironically, was practically created by the NSA itself and its anti-encryption policies from 20 years ago.The NSA's site was just the guinea pig to demonstrate a newly-disclosed internet flaw called FREAK.The bug, first disclosed on Monday by Akamai, allows an attacker to intercept a supposedly secure connection between people using Android or Apple devices and thousands, if not millions, of websites. This gives the hackers the chance to impersonate said website and steal confidential data like passwords and logins.Now, as crypto expert Matthew Green correctly pointed out, this wasn't really a "hack." Mounting a man-in-the-middle attack against NSA.gov is not the same as hacking the NSA (as an always-appropriate XKCD cartoon illustrates).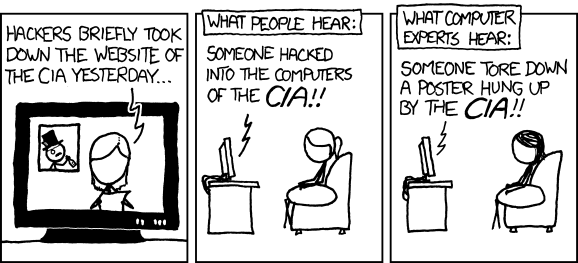 The researchers were actually just trying to make a point, and to show how dangerous this new bug is. But the choice of the target wasn't random."In the current climate, it felt like the appropriate website to mount a man-in-the-middle attack on," Karthikeyan Bhargavan, one of the lead researchers who discovered the bug, told Motherboard.Bhargavan was obviously referring to the Edward Snowden revelations, the current debate over encryption, but also to the so-called Crypto Wars of the 1990s. Back then, the NSA and the US government, afraid that the popularization of encryption software would harm national security, pushed for export controls that forced security firms to ship weaker encryption protocols outside of the United States.In other words, they pushed for encryption backdoors, and roughly two decades later, that policy decision has left the door open for this bug.That's the lesson here. Encryption backdoors "never quite work out the way you want them to," Green, the cryptography professor at Johns Hopkins University, wrote in a blog post about the bug.FREAK is a "good example of what can go wrong when government asks to build weaknesses into security systems," wrote Ed Felten, another respected professor of computer science at Princeton University.The hacker also needs "a certain amount of technical finesse," according to Karthikeyan, and access to "cutting-edge" tools to factor the keys. But once they break the keys, that's game over.
The researchers were actually just trying to make a point, and to show how dangerous this new bug is. But the choice of the target wasn't random."In the current climate, it felt like the appropriate website to mount a man-in-the-middle attack on," Karthikeyan Bhargavan, one of the lead researchers who discovered the bug, told Motherboard.Bhargavan was obviously referring to the Edward Snowden revelations, the current debate over encryption, but also to the so-called Crypto Wars of the 1990s. Back then, the NSA and the US government, afraid that the popularization of encryption software would harm national security, pushed for export controls that forced security firms to ship weaker encryption protocols outside of the United States.In other words, they pushed for encryption backdoors, and roughly two decades later, that policy decision has left the door open for this bug.That's the lesson here. Encryption backdoors "never quite work out the way you want them to," Green, the cryptography professor at Johns Hopkins University, wrote in a blog post about the bug.FREAK is a "good example of what can go wrong when government asks to build weaknesses into security systems," wrote Ed Felten, another respected professor of computer science at Princeton University.The hacker also needs "a certain amount of technical finesse," according to Karthikeyan, and access to "cutting-edge" tools to factor the keys. But once they break the keys, that's game over. For now the list of potential victims includes Macs (though Apple has already announced that it will roll out a fix next week), and some Android smartphones. While tech companies and website owners rush to issue a patch, you can test if you're vulnerable at freakattack.com.As for the NSA, the site is still unpatched. Vanee Vines, a spokesperson for the agency, did not respond to Motherboard's request for comment.Karthikeyan said that perhaps the NSA didn't bother patching yet because "they didn't care enough about it" since the site doesn't contain or host sensitive information. But Karthikeyan also noted that the NSA has a careers website, and with this bug, someone could potentially steal the username and passwords of would-be NSAers, and access their job applications.So perhaps, Karthikeyan added, the NSA "should be more careful."
For now the list of potential victims includes Macs (though Apple has already announced that it will roll out a fix next week), and some Android smartphones. While tech companies and website owners rush to issue a patch, you can test if you're vulnerable at freakattack.com.As for the NSA, the site is still unpatched. Vanee Vines, a spokesperson for the agency, did not respond to Motherboard's request for comment.Karthikeyan said that perhaps the NSA didn't bother patching yet because "they didn't care enough about it" since the site doesn't contain or host sensitive information. But Karthikeyan also noted that the NSA has a careers website, and with this bug, someone could potentially steal the username and passwords of would-be NSAers, and access their job applications.So perhaps, Karthikeyan added, the NSA "should be more careful."
Advertisement
Advertisement
In this particular case, the culprits are the RSA-EXPORT Keys or Suites.These were weaker 512-bit keys used only outside the United States, where the law allowed for stronger crypto. Many sites abandoned those keys once the export controls restrictions were dropped. But surprisingly, a large amount of websites were still using them, and were thus vulnerable to FREAK, according to another group of researchers at University of Michigan who performed a scan of the Internet to do a census.As of Tuesday, according to their scan, more than 36% of websites that support web encryption (TLS or SSL) were vulnerable, including 12.2% of the top 1 millions websites in the world, including bloomberg.com, americanexpress.com, as well as the NSA website and the FBI's site for anonymous tips."We didn't think there'd be sites supporting this really ancient export cipher suites," said Karthikeyan, who works for a French research group called Prosecco, which is part of Paris-based INRIA.The bug also affected a Facebook website (connect.facebook.net) which hosts the script for Facebook's "Like" and login button that are included in innumerable websites on the Internet."That's a big chunk of the Internet," Karthikeyan said.The good news is that this is not a trivial attack. A hacker trying to exploit this needs to be on an insecure network, such as a coffee shop WiFi, and exploit a vulnerable site. The hacker also needs to target a victim who is on the same network, and using a vulnerable device."In the current climate, it felt like the appropriate website to mount a man-in-the-middle attack on."
Advertisement

