Image: Malwarebytes
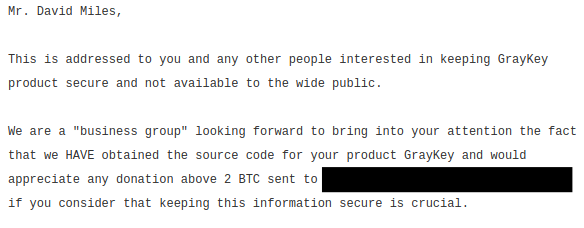
This is part of an ongoing Motherboard series on the proliferation of phone cracking technology, the people behind it, and who is buying it. Follow along here .Law enforcement agencies across the country are buying or have expressed interest in buying GrayKey, a device that can unlock up-to-date iPhones. But Grayshift, the company that makes the device, has attracted some other attention as well.Last week, an unknown party quietly leaked portions of GrayKey code onto the internet, and demanded over $15,000 from Grayshift—ironically, the price of an entry-level GrayKey—in order to stop publishing the material. The code itself does not appear to be particularly sensitive, but Grayshift confirmed to Motherboard the brief data leak that led to the extortion attempt."Mr. David Miles," the extortionists' first message, published on Thursday, reads, addressing a co-founder of Grayshift. "This is addressed to you and any other people interested in keeping GrayKey product secure and not available to the wide [sic] public."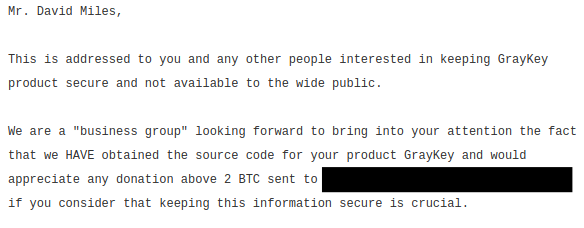 The site hosting the message has since deleted the post, but a Google cached version is still available, and a second message, published a day later, is online at the time of writing."We are a 'business group' looking forward to bring into your attention the fact that we HAVE obtained the source code for your product GrayKey and would appreciate any donation above 2 BTC [~$19,000 on Tuesday]," both messages continue. Both then paste different selections of apparent GrayKey code.Indeed, Grayshift told Motherboard in a statement "Due [to] a network misconfiguration at a customer site, a GrayKey unit's UI was exposed to the internet for a brief period of time earlier this month.""During this time, someone accessed the HTML/Javascript that makes up our UI. No sensitive IP or data was exposed, as the GrayKey was being validation tested at the time. We have since implemented changes to help our customers prevent unauthorized access," the statement added.Using the computer search engine Shodan, Motherboard found a seemingly exposed GrayKey device, broadcasting similar chunks of code to the open internet."To brute force a complex alphanumeric passcode, upload a custom password dictionary. If a dictionary is not uploaded, GrayKey will not attempt to brute force custom alphanumeric passcodes," one section of the apparent device's code reads.At the time of writing, the Bitcoin addresses the extortionists gave for Grayshift to deposit the payment have received no funds. The unknown party also included a separate address for "wild bidders" who want all of the GrayKey information to be released. This address has also seen no payment.Motherboard found regional police forces and the State Department have purchased GrayKeys, and the FBI is interested in purchasing the tech, along with other law enforcement bodies.Update: This piece has been updated to include information from Shodan.Get six of our favorite Motherboard stories every day by signing up for our newsletter.
The site hosting the message has since deleted the post, but a Google cached version is still available, and a second message, published a day later, is online at the time of writing."We are a 'business group' looking forward to bring into your attention the fact that we HAVE obtained the source code for your product GrayKey and would appreciate any donation above 2 BTC [~$19,000 on Tuesday]," both messages continue. Both then paste different selections of apparent GrayKey code.Indeed, Grayshift told Motherboard in a statement "Due [to] a network misconfiguration at a customer site, a GrayKey unit's UI was exposed to the internet for a brief period of time earlier this month.""During this time, someone accessed the HTML/Javascript that makes up our UI. No sensitive IP or data was exposed, as the GrayKey was being validation tested at the time. We have since implemented changes to help our customers prevent unauthorized access," the statement added.Using the computer search engine Shodan, Motherboard found a seemingly exposed GrayKey device, broadcasting similar chunks of code to the open internet."To brute force a complex alphanumeric passcode, upload a custom password dictionary. If a dictionary is not uploaded, GrayKey will not attempt to brute force custom alphanumeric passcodes," one section of the apparent device's code reads.At the time of writing, the Bitcoin addresses the extortionists gave for Grayshift to deposit the payment have received no funds. The unknown party also included a separate address for "wild bidders" who want all of the GrayKey information to be released. This address has also seen no payment.Motherboard found regional police forces and the State Department have purchased GrayKeys, and the FBI is interested in purchasing the tech, along with other law enforcement bodies.Update: This piece has been updated to include information from Shodan.Get six of our favorite Motherboard stories every day by signing up for our newsletter.
Advertisement
The GrayKey can unlock modern iPhones, including models running iOS 11.3 and the iPhone X. The device works by brute-forcing possible passcode combinations, and can break through 4 digits in around two hours, and 6 digits in three days or longer, according to leaked details published by cybersecurity firm Malwarebytes.The code the extortionists posted isn't all that interesting. Instead, it seems to be for operating the display on the GrayKey that provides messages to a user."Waiting for GrayKey…" one line reads, with the code suggesting that the display will then show a "wait image," something similar to a loading icon.Got a tip? You can contact this reporter securely on Signal on +44 20 8133 5190, OTR chat on jfcox@jabber.ccc.de, or email joseph.cox@vice.com.
Advertisement
