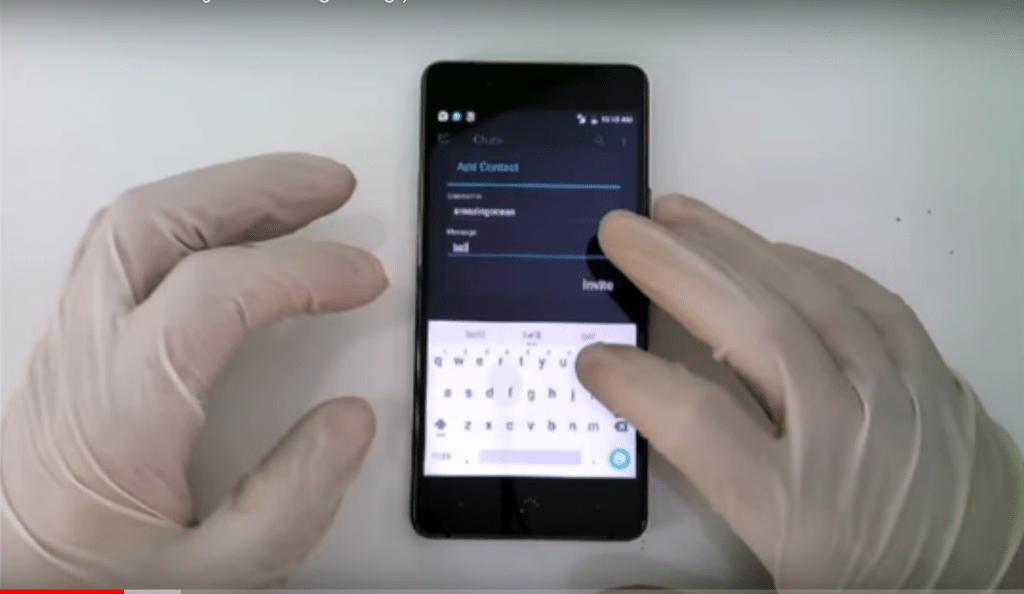
“Inside information has been leaked!” the caption beneath an anonymous video, uploaded last month to YouTube, reads. In the clip, someone wearing white latex gloves taps on a phone’s screen, allegedly showing a security issue with the device, while synth-heavy dance music pumps in the background. The phone is made by EncroChat, a firm which sells custom smartphones that it says are more secure than mass-market phones.
The 10 minute long video, complete with theatrical “access granted” graphics, claims to show how someone can extract data from an EncroChat phone, something that should be difficult due to the device’s encryption. A post on EncroChat Hacked, an anonymous blog that shared the video, says “all police stations” can replicate the attack. Clearly, the post is talking to one of EncroChat’s alleged customer bases: criminals.
Videos by VICE
“What we just showed you was just the beginning,” text in the video reads.
This is the latest chapter in a fierce rivalry playing out across the secure phone industry, whose products are in use by organized criminal groups. The industry is rife with constant infighting and accusations ricocheted between different firms.
The security-focused devices EncroChat and others sell are typically either Android devices with a customized operating system that are preloaded with apps for secure messaging and perhaps file storage, or BlackBerry phones with the capability to send PGP encrypted emails. Some phones even have the microphone and camera removed. They are ostensibly for the security- and privacy-conscious, but previous reporting has shown that many of these companies’ customers are involved in organized crime.
EncroChat sits alongside a slew of other similar companies in this space: MPC, Phantom, Ciphr, Myntex. To be clear, some firms are legitimate businesses looking to provide a device for the security or privacy conscious. Others, though, are much more opaque, with hard to track down owners, and advertisements on crime-focused websites. Some companies in this space have even allegedly hacked their rivals. Law enforcement agencies have shuttered a number of secure phone companies, including Ennetcom and PGPSure in the Netherlands. In Ennetcom’s case, authorities previously said they found in the company’s users’ messages evidence for investigations into assassinations, armed robbery, drug trafficking, money laundering, attempted murder, and other organized crime.
That’s the context of the recent YouTube video and anonymous blog posts: from all appearances, the white gloves are likely being worn by a competitor. An industry source, who Motherboard granted anonymity to discuss internal industry developments, said some EncroChat customers have stopped using the company’s phones because of the recent video.
EncroChat didn’t just leave the video, which has now been viewed nearly 6,000 times, to spread among the secure phone community without biting back, though. Just under a week later, EncroChat published its own video and blog, allegedly showing an attack on a device running Samsung Knox, Samsung’s security-focused operating system, which obtained the target’s password and chat logs. (A second industry source, who asked to remain anonymous to discuss internal industry developments, said that this video appears to be fake).
“EncroChat does not post anonymous fake videos and hide behind false personas spreading lies and rumors about competitors. Our organization stands behind this video and we post it on our corporate website,” EncroChat’s blog post reads.
Samsung did not respond to a request for comment. Neither did EncroChat.
EncroChat apparently went one step further, and blocked its own customers from communicating with devices from Ciphr, Phantom, and Myntex, the blog post reads. EncroChat also dumped a list of each company’s domains, allowing others to map out web infrastructure that belongs to the firms. The blog EncroChat Hacked then responded in turn, claiming that EncroChat may be developed by only one person, implying that the quality of the code may be inferior to other products.
This practice of trying to discredit competitors through hastily uploaded YouTube videos and bold claims on anonymous blog posts stretches back further than these most recent developments. In one 2016 clip, a narrator claims that EncroChat and Myntex are federal informants on a “massive scale,” and that EncroChat’s device includes software that spies on the user. Again, the video is dubious, and the creator doesn’t provide any concrete evidence for these claims.
“It’s only going to get dirtier,” the first industry source told Motherboard.
More
From VICE
-

Photo: Malte Mueller / Getty Images -

Photo: Maria Saifutdinova / Getty Images -

Photo: master1305 / Getty Images -

Photo: Eoneren / Getty Images