For the first time, a judge has thrown out evidence obtained via a piece of FBI malware. The move comes from a cased affected by the FBI’s seizure of a dark web child pornography site in February 2015, and the subsequent deployment of a network investigative technique (NIT)—the agency’s term for a hacking tool—in order to identify the site’s visitors.
“Based on the foregoing analysis, the Court concludes that the NIT warrant was issued without jurisdiction and thus was void ab initio,” Judge William G. Young of the District of Massachusetts writes in an order. “It follows that the resulting search was conducted as though there were no warrant at all.”
Videos by VICE
“Since warrantless searches are presumptively unreasonable, and the good-faith exception is inapplicable, the evidence must be excluded,” it continues.
Young’s order came in response to a motion to suppress from the lawyers of Alex Levin, who was arrested as part of the investigation into the child pornography site Playpen. After seizing the site, the FBI ran Playpen from a government facility from February 20 to March 4, 2015, and used a NIT to obtain over a thousand IP addresses for US-based users of the site, and at least 3000 for users abroad, according to Motherboard’s investigations.
Young’s move hinges around the one warrant used to authorise all of these computer intrusions. Lawyers have raised issues with it before—Colin Fieman, a defender in a related case, previously told Motherboard that it “effectively authorizes an unlimited number of searches, against unidentified targets, anywhere in the world.” The Electronic Frontier Foundation filed a strongly-worded amicus brief in another affected case, and called the warrant “unconstitutional.”
“This is the first time a court has ever suppressed anything from a government hacking operation,” Christopher Soghoian, principal technologist at the American Civil Liberties Union (ACLU), told Motherboard in an encrypted phone call. (Soghoian has been called as an expert by the defense in another affected case.)
Other judges have blocked parts of hacking operations before. In 2013, a judge denied the FBI a hacking warrant that would have authorised the agency to collect chat logs, web history and other data from the target laptop, as well as turn on the suspect’s web camera.
Lawyers from other affected cases around the country are sure to be following this latest order closely.
UPDATE: Peter Carr, a spokesperson for the Department of Justice, sent a statement.
“We are disappointed with the court’s decision and are reviewing our options. The decision highlights why the government supports the clarification of the rules of procedure currently pending before the Supreme Court to ensure that criminals using sophisticated anonymizing technologies to conceal their identities while they engage in crime over the Internet are able to be identified and apprehended.”
More
From VICE
-

Photo: Gandee Vasan / Getty Images -

Photo: duncan1890 / Getty Images -

Photo: Jorge Garc'a /VW Pics/Universal Images Group via Getty Images -
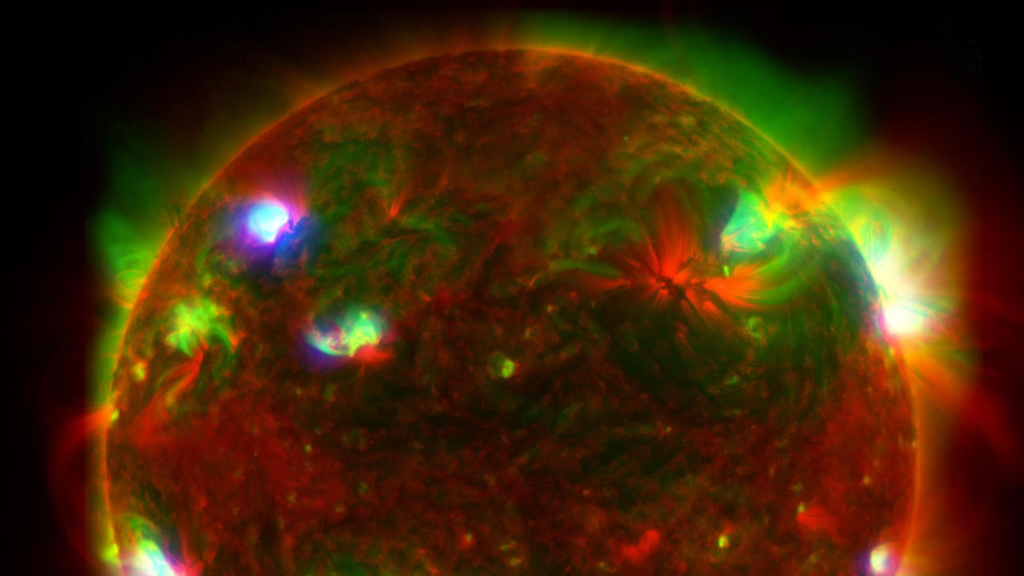
Three-Telescope View of the Sun. Photo: NASA