Apple just announced that it will send special devices that make it easier to find flaws and vulnerabilities in its mobile operating system iOS to iPhone hackers that apply and qualify for a program the company announced last year. The program might make some hackers less likely to engage in the underground market for stolen prototype iPhones hackers currently use to research iPhone security, and encourage them to share their findings with Apple.
In a new website published on Wednesday, Apple wrote that the program “features an iPhone dedicated exclusively to security research, with unique code execution and containment policies.”
Videos by VICE

It’s called the Security Research Device Program. Security researchers can apply for it starting today and Apple told Motherboard that if they qualify they will receive the devices soon. Apple doesn’t have a goal in terms of how many of these devices it wants to send out, and all you need to qualify is having a public track record of security research, not only on iPhone but also on other popular devices and software like Android phones, Windows, or Linux.
Do you work or did you use to work at Apple? Do you trade prototypes or do research on iOS? We’d love to hear from you. You can contact Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, OTR chat at lorenzofb@jabber.ccc.de, or email lorenzofb@vice.com
If a researcher qualifies, Apple will loan them one of these special devices, and the researcher will be legally bound to share any bugs they find with Apple so that the company can fix them. Apple is also providing a special online forum where qualified researchers can share findings, tips, and talk to Apple engineers.
The idea, Apple explained in a background call, is to make the bar to find vulnerabilities in iOS a little lower. Right now, it’s so hard to find vulnerabilities in iPhones that there’s a thriving market for stolen prototype iPhones that have security features disabled and make hacking them easier.
Subscribe to our new cybersecurity podcast, CYBER.
More
From VICE
-

Illustration by Reesa. -

Georgiana Dallas/WWE via Getty Images -

Screenshot: Netflix -
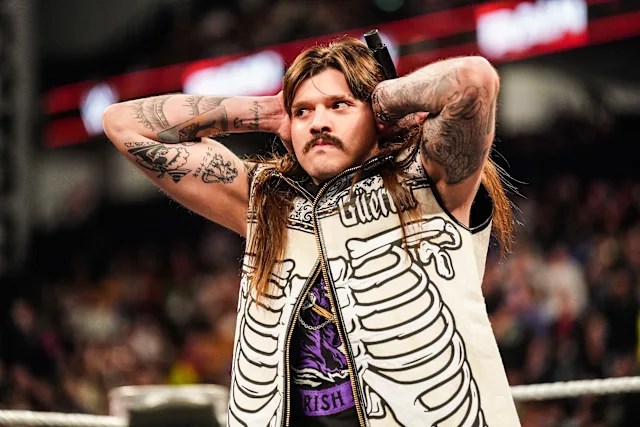
WWE
