In what’s becoming a bit of a trend in modern technical incompetence, yet another company has left oodles of private company data sitting openly accessible on an Amazon cloud server.
According to a new report by the security researchers at UpGuard, a Washington-based ISP by the name of Pocket iNet left 73 gigabytes of essential operational data publicly exposed in a misconfigured Amazon S3 storage bucket for months.
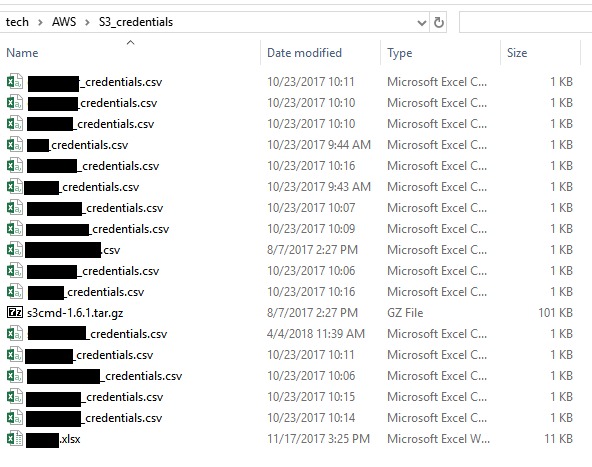
Said bucket, named “pinapp2,” contained the “keys to the kingdom,” according to the security firm, including internal network diagramming, network hardware configuration photos, details and inventory lists—as well as lists of plain text passwords and AWS secret keys for Pocket iNet employees.
Like so many other companies, the ISP was somewhat sluggish when initially contacted by Upguard and informed about the massive privacy breach. Upguard says the firm contacted Pocket iNet on October 11 of this year, the same day the exposed bucket was discovered, but the ISP took an additional week before the data was adequately secured.
Videos by VICE

“Seven days passed before Pocket iNet finally secured the exposure,” noted the firm. “Due to the severity of this exposure, UpGuard expended significant effort during those seven days, repeatedly contacting Pocket iNet and relevant regulators, including using contact information found within the exposed dataset.”
ISPs are particularly juicy targets for bad actors given their insight into every shred of data that touches their networks, and have been designated as part of the US Critical Infrastructure by the Department of Homeland Security.
According to UpGuard, the list of plain text passwords was particularly problematic, given it provided root admin access to the ISP’s firewalls, core routers and switches, servers, and wireless access points.
“Documents containing long lists of administrative passwords may be convenient for operations, but they create single points of total risk, where the compromise of one document can have severe and extensive effects throughout the entire business,” noted UpGuard.
“If such documents must exist, they should be strongly encrypted and stored in a known secure location,” said the firm.
“Unfortunately, a single folder of PocketiNet’s network operation historical data (non-customer) was publicly accessible to Amazon administrative users,” the ISP said in a statement to Motherboard. “It has since been secured.”
“We appreciate being alerting us to this error,” The company added. “PocketiNet is currently conducting a comprehensive network review to guarantee no additional data is compromised. We have also begun a complete analysis of operating procedures to ensure no future errors occur.”
The ISP certainly isn’t alone when it comes to leaving sensitive company or consumer data openly-accessible to the outside world.
Verizon recently made headlines (also courtesy of UpGuard) after one of its customer service vendors left the personal data of around 6 million consumers openly accessible on an Amazon server without adequate password protection. Time Warner Cable (since acquired by Charter) similarly left 4 million user records sitting in an openly-accessible Amazon bucket.
And last year, a GOP data analytics firm was also soundly ridiculed after it left the personal data of around 198 million citizens (read: most of you) similarly just sitting on an Amazon server without protection, providing anybody with an internet connection access to the GOP data sets used to power Donald Trump’s presidential victory,
Businesses will spend nearly a trillion dollars between 2017-2021 on cybersecurity, with a heavy focus on combating malware, intrusion detection, and other threats. Yet despite the best efforts of security researchers like UpGuard’s Chris Vickery (who has been exposing this issue for years), simple misconfiguration errors still, somehow, aren’t getting the attention they deserve.
Update: This article has been updated with comment from Pocket iNet.
More
From VICE
-

Screenshot: X @FF_XIV_EN, Square Enix -

WC Fields (Photo by Universal/Getty Images) -

(Photo by Scott Dudelson/Getty Images) -

Photo by Fight For The Future
